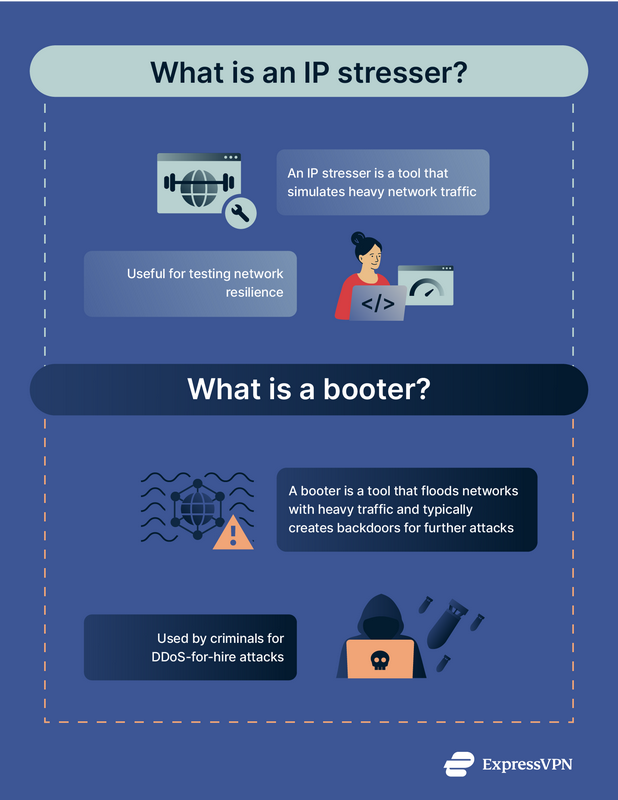
An IP stresser is a service that does a cardiovascular test to evaluate the strength of a network or web server by imitating a DDoS attack. When made use of for legitimate objectives, IP stressors aid IT groups figure out exactly how well a system can take care of the extra lots or anxiety of an attack. Given that IP stresser services in of themselves are not prohibited, cybercriminals typically camouflage their DDoS booter solutions as IP stresser services provided online.
Just how do DDoS booters function?
Supplying bogus use an IP stresser, DDoS booters are DDoS-for-hire services that can be leased on the dark internet by people with little to no experience in releasing cyberattacks. Compared to the price of establishing a botnet with thousands or countless malware-infected gadgets, leasing a DDoS booter is incredibly inexpensive. Solutions might set you back less than $25 a month, commonly payable through PayPal, or cryptocurrencies, and some stressor sites allow a trial which gives the individual accessibility to a restricted function of assault dimension, period, and vectors selected. Booter sites might package their services as subscriptions that consist of tutorials and user assistance.At site free stresser from Our Articles Consequently, DDoS booters are prominent with cybercriminals in training, known as script kids or skiddies, that are starting to check out just how cybercrime functions. DDoS booters are likewise utilized by skilled hackers who utilize DDoS attacks as a cover or entry factor for releasing a lot more devastating assaults developed to gain access to a network to steal data or money.
What is a DDoS booter vs. a botnet?
Botnets are a collection of malware-infected or exploited tools that can be utilized to execute DDoS attacks or other sorts of cyberthreats. DDoS booters provide DDoS assaults as an on-demand solution, making use of either a botnet or an opponent’s own collection of a lot more powerful servers.
What kinds of assaults do DDoS booters execute?
Cyberpunks might lease booters to execute a variety of DDoS attacks.
- Volumetric attacks. These strikes purpose to flood a target with high quantities of web traffic to eat its readily available bandwidth, tiring resources and making the network or web site inaccessible.
- TCP out-of-state, aka state-exhaustion, attacks. These assaults overwhelm a target’s resources by exploiting the stateful nature of TCP (Transmission Control Protocol) to exhaust offered connections and take in system or network sources.
- Application-layer assaults. These consist of Slowloris attacks and various other HTTP floodings that wear down a server or API resources. DNS pseudo-random subdomain (PRSD) assaults are a type of application strikes, yet focus on the DNS protocol (vs. HTTP procedures, which are more conventional application assaults).
- Fragmentation strikes. These attacks send fragmented IP packages that should be reconstructed, eating a huge amount of the target’s resources and exhausting its ability to deal with extra requests.
- DNS reflection or amplification strikes. These strikes enhance an opponent’s efforts by manipulating susceptabilities in DNS servers. Attackers send out requests to DNS servers that trigger responses having large amounts of info to bewilder a targeted IP address.
- IoT-based assaults. Attackers may jeopardize vulnerabilities in Web of Points (IoT) tools to develop botnets for introducing DDoS strikes that can create substantial quantities of web traffic.
Are DDoS booters prohibited?
Providing or renting DDoS booters is unlawful. Law enforcement, including the U.S. Department of Justice (DOJ) and global police, are proactively working to take down booter websites and apprehend the people who offer and use them (Operation PowerOFF, for example).
What’s the most effective protection versus a DDoS booter?
Organizations can prevent DDoS booter services with the same multilayered cybersecurity steps they utilize to minimize DDoS assaults. Ideal techniques for DDoS protection consist of:
- Use a DDoS mitigation solution. A trustworthy DDoS reduction service provider can assist to detect and strain destructive web traffic during a DDoS assault, stopping traffic from reaching web servers while making certain legit customers can still get to a network or web site. Cloud DDoS rubbing solutions are a strategy commonly deployed.
- Screen web traffic for abnormalities. Surveillance devices that identify and analyze website traffic patterns can assist to identify what normal web traffic appears like and spot uncommon web traffic that might become part of a DDoS assault.
- Release price limiting. Rate-limiting tools reduce the influence of a DDoS strike by restricting the number of demands from a solitary IP address or blocking website traffic from IP addresses that are understood to be harmful.
- Increase capability. Scaling up transmission capacity, including load-balancing capacities, and enhancing repetitive systems can help to soak up the sudden spike of website traffic during a DDoS assault.
- Use a material delivery network (CDN). CDNs assist distribute web traffic geographically across several web servers and data centers, supplying additional network ability that can soak up and alleviate DDoS attacks.
- Release firewall programs and IPS. Firewall programs and breach avoidance systems (IPS) that are upgraded with the most up to date hazard knowledge can strain destructive website traffic and block suspicious IP addresses.